Imagine waking up to find that your business is suddenly breaking the law in eight different states, despite not changing a single line of code. That is the reality for many companies in 2026. We have entered an era where Privacy Protocol Regulations is the complex system of legal frameworks that dictate how organizations must handle personal data to protect individual privacy. It is no longer just about one big law like the GDPR; it is now a fragmented puzzle of state and national rules that change depending on where your user is sitting.
For those in the blockchain and tech space, this is a nightmare. How do you reconcile a permanent, immutable ledger with a legal requirement to "delete" data? The gap between technical reality and legal mandate is widening, and the penalties for ignoring it are getting steeper. If you are operating across borders or even just across US state lines, you need a strategy that moves beyond a simple "Privacy Policy" page on your website.
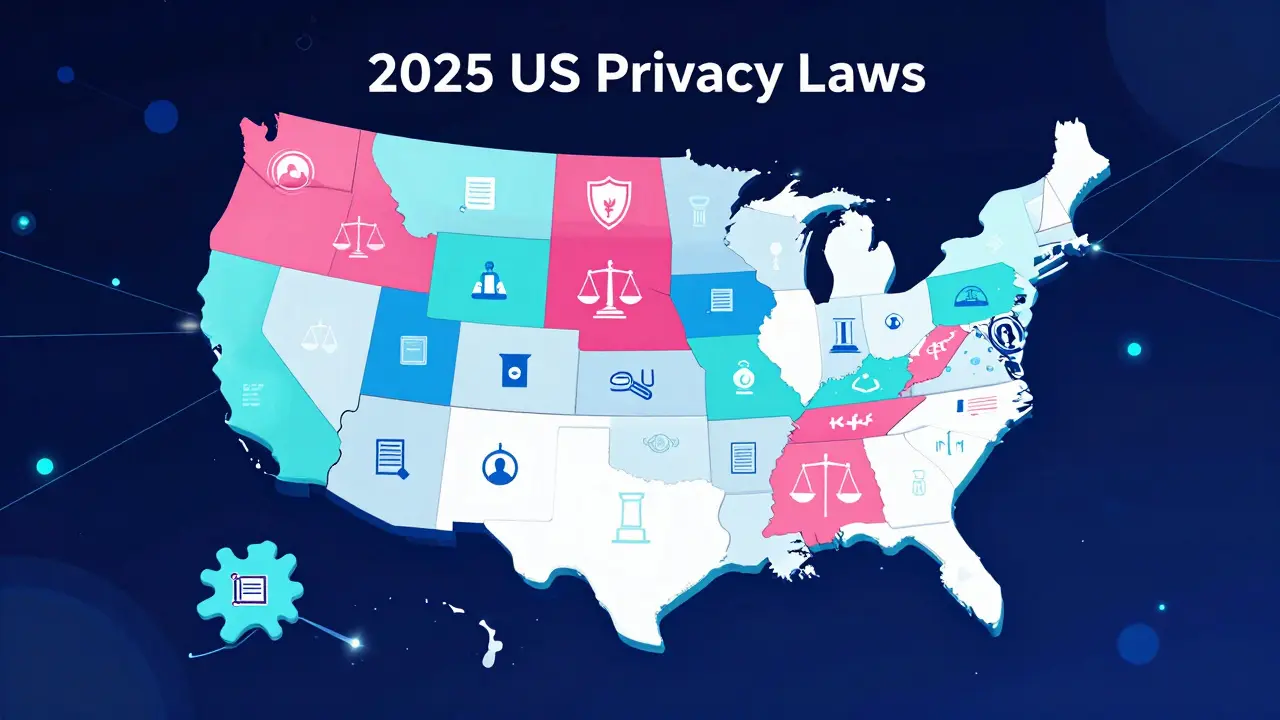
The 2025 US State Law Explosion
Throughout 2025, the US saw a massive wave of new legislation. Eight new state laws went live, turning the legal landscape into a patchwork. We are talking about the Iowa Consumer Privacy Act (ICPA), the Delaware Personal Data Privacy Act (DPDPA), and others like those in New Jersey, Nebraska, Tennessee, Minnesota, and Maryland.
The problem isn't just that there are more laws, but that they don't agree on the details. For example, if you're dealing with the Maryland Online Data Privacy Act (MODPA), you might have a generous 60-day cure period until April 2027. But if you're operating in Delaware, the rules are much tighter. Delaware's law is particularly aggressive because it hits businesses that process data for as few as 35,000 consumers-a tiny threshold compared to other states.
This fragmentation means you can't have one "standard" protocol. You need a dynamic system that knows if a user is in Iowa (where they have fewer opt-out rights) or Delaware (where you must provide a detailed list of every third party receiving their data). It is a logistical hurdle that requires real-time data mapping.
Comparing the Compliance Burden
To understand why this is so stressful for operations teams, look at how the specifics vary. One state might give you 90 days to respond to a request, while another demands it in 45. These aren't just suggestions; they are hard deadlines with financial teeth.
| State Law | Response Timeline | Key Distinct Feature | Max Penalty |
|---|---|---|---|
| Delaware (DPDPA) | 45 Days | Very low applicability threshold (35k users) | $10,000 per violation |
| Iowa (ICPA) | 90 Days | Opt-out rights limited to data sales only | $7,500 per violation |
| Maryland (MODPA) | Varies | Extended 60-day cure period until 2027 | Varies by violation |
| New Jersey (NJCPA) | Standard | 30-day cure period until July 2026 | Varies by violation |
Global Pressure and the Digital Border
If you think the US is messy, the global stage is even more chaotic. India launched the Digital Personal Data Protection Act (DPDPA), which focuses heavily on the concept of "fiduciary responsibility." This means if you process data for someone in India, you aren't just a service provider; you are legally responsible for that data as if it were a trust.
Meanwhile, the European Union is layering new requirements on top of the GDPR. We now have the EU AI Act and DORA (Digital Operational Resilience Act), which force companies to prove their technical infrastructure can withstand shocks while keeping data private. For a blockchain project, this means your smart contracts and node distributions might actually fall under "operational resilience" audits. You can't just say "the code is law" anymore; the law is now auditing your code.
The Technical Struggle: Implementing DSARs
The core of most of these laws is the Data Subject Access Request (DSAR) a mechanism allowing individuals to request a copy, correction, or deletion of their personal information from a company's records.
In a traditional database, a DSAR is a query. In a decentralized environment, it's a crisis. If a user in Delaware demands the deletion of their data, but that data is hashed into a block on a public chain, you have a fundamental conflict. This is why many protocols are moving toward "off-chain" storage for personal identifiers, using the blockchain only for verification hashes. If you store PII (Personally Identifiable Information) directly on-chain, you are essentially building a compliance time bomb.
To survive, organizations are adopting automated preference centers. Instead of a manual email process, they use software that automatically detects the user's jurisdiction and applies the correct legal logic-giving the Maryland user their cure period while holding the Delaware operation to a 45-day clock.
The FCC and the New Rules of Communication
Privacy doesn't just stop at data storage; it extends to how you reach out to people. The Telephone Consumer Protection Act (TCPA) a federal law that restricts the use of automatic telephone dialing systems and prerecorded voices for telemarketing has updated its rules for 2025.
If you use automated bots for marketing or alerts, the "one-to-one consent" rule is now critical. You can't just rely on a blanket checkbox during sign-up. The FCC now requires specific, clear consent for texting and calling. If your protocol uses automated SMS notifications for transaction alerts, you need to ensure your opt-in flow is airtight, or you'll be facing class-action lawsuits that make state privacy fines look like pocket change.

Building a Future-Proof Privacy Stack
So, how do you actually manage this without hiring a thousand lawyers? You stop treating privacy as a legal chore and start treating it as a technical feature.
- Data Discovery: You cannot protect what you cannot find. Use automated tools to map where data flows across your entire ecosystem.
- Modular Compliance: Build your privacy logic as a set of pluggable modules. When a new law passes in another state, you simply add a new "rule set" rather than rewriting your whole data architecture.
- Privacy by Design: Collect the absolute minimum data needed. If you don't have the data, you can't be fined for losing it or failing to delete it.
- Automated Workflows: Move DSARs and opt-outs into a self-service portal. Manual processing is where the 45-day deadlines get missed.
The trend is clear: we are moving toward a world of "hyper-localization." Your software needs to be as aware of the user's legal geography as it is of their IP address. The companies that win won't be the ones with the biggest legal teams, but the ones with the most flexible data architecture.
What happens if my business is a nonprofit?
In the past, nonprofits often had a free pass, but that is changing. For example, Delaware's DPDPA applies to nonprofits without exemption. If you handle consumer data in Delaware, you must comply regardless of your tax status.
Does HIPAA protect me from state privacy laws?
Not entirely. While HIPAA covers health data, state laws like the DPDPA often cover "non-protected" data. This includes things like a patient's contact information used for appointment reminders, which might still fall under state privacy regulations.
How long do I have to respond to a data deletion request?
It depends entirely on the state. Iowa gives you a generous 90 days, while Delaware requires a response within 45 days. Always aim for the shortest common denominator to avoid penalties.
What is a "cure period" in privacy law?
A cure period is a grace period where a company can fix a violation after being notified before the government imposes a fine. These are disappearing; for instance, Delaware's 60-day cure period ended on January 1, 2026.
How does the EU AI Act affect data privacy?
The EU AI Act adds a layer of governance over how data is used to train models. It requires transparency and strict risk management, meaning you must be able to prove that the data used in your AI protocols was obtained legally and ethically.
Next Steps for Implementation
If you are just starting to audit your protocols, start with a gap analysis. Compare your current data storage methods against the Delaware and India frameworks, as these are currently among the most stringent. If you fail those, you're likely failing others too.
For blockchain developers, the immediate priority is moving toward Zero-Knowledge Proofs (ZKPs). By proving a statement is true without revealing the underlying data, you can satisfy the "privacy" requirement of the law without ever actually storing the sensitive data on a public ledger. This is the only sustainable way to bridge the gap between decentralization and regulation.

Author
Ronan Caverly
I'm a blockchain analyst and market strategist bridging crypto and equities. I research protocols, decode tokenomics, and track exchange flows to spot risk and opportunity. I invest privately and advise fintech teams on go-to-market and compliance-aware growth. I also publish weekly insights to help retail and funds navigate digital asset cycles.